If youre evaluating healthcare data integration tools, youre probably feeling the same pressure I see everywhere: more data sources, more standards, more stakeholders, and less patience for brittle interfaces. The good news? The market has matured. The bad news? The choices can still be confusing (and expensive).
So lets make it practical. I’ll walk you through what these tools actually do, what capabilities matter in the real world, the architectures that hold up at enterprise scale, and a no-nonsense way to choose a platform without getting trapped in vendor buzzwords.
What are healthcare data integration tools?
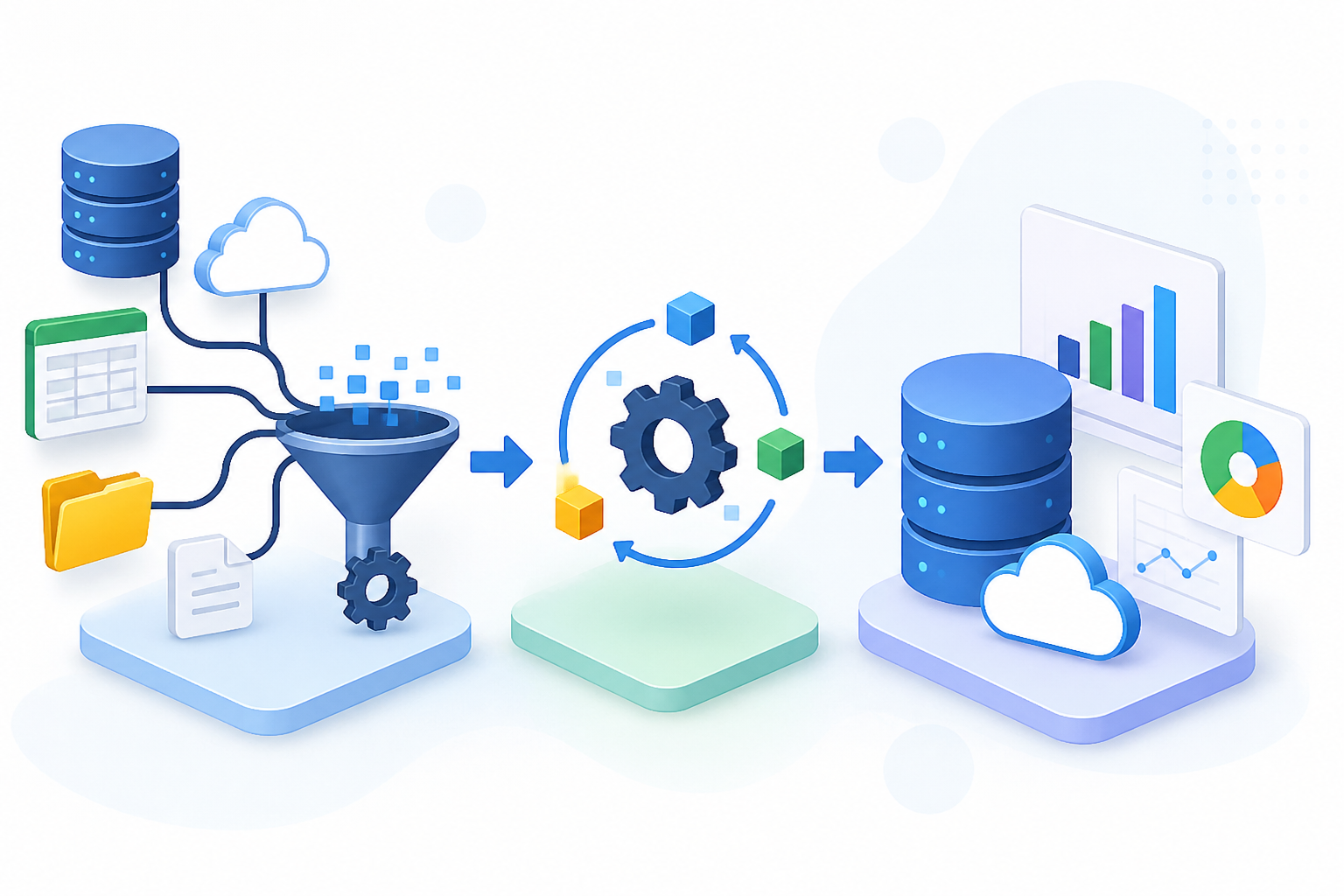
Healthcare data integration tools are software products that connect systems, move data between them, and make that data usable across workflows. Think: EHR to lab, imaging to radiology viewer, claims to analytics, device feeds to care management, and everything in between.
But integration isnt just “send message from A to B.” The best modern healthcare data integration tools handle mapping, validation, identity matching, security controls, monitoring, and reliable delivery. Because when a lab result doesnt arrive, its not an IT issue. Its a patient-care issue.
Common use cases
Youll see the same repeat offenders across most health systems and digital health vendors. Different logos, same patterns.
- EHR and EMR integration: ADT feeds, orders, results, scheduling, clinical documents, and API-based workflows like SMART on FHIR launches.
- Labs: HL7 v2 ORU results, LOINC mapping, reflex testing rules, and critical result notifications with acknowledgments.
- Imaging: DICOM studies, modality worklists, imaging metadata, and routing to PACS or cloud archives.
- Claims and eligibility: X12 270/271, 276/277, 837, 835, plus prior auth workflows that mix X12, portals, and APIs.
- Remote patient monitoring: Device telemetry, thresholds, patient-reported outcomes, and alerting to care teams with audit trails.
- EMS and hospital handoff: Pre-arrival notifications, ePCR summaries, and pushing key data into ED workflows fast.
And yes, these use cases often overlap. A single referral workflow might touch the EHR, fax replacement, payer APIs, a CRM, and your analytics stack. Fun, right?
Integration vs interoperability vs data warehousing
People mix these terms up constantly. I dont blame them.
Integration is the act of connecting systems and moving data. It’s operational. It’s about “make this workflow work.”
Interoperability is the ability for systems to exchange and meaningfully use the data. Standards help, but governance and semantics matter just as much. You can send HL7 all day and still be non-interoperable if your mappings are messy.
Data warehousing is about storing and analyzing data over time. It’s optimized for reporting, BI, quality measures, population health, and ML. Warehouses often consume integrated feeds, but they dont replace real-time integration for care delivery.
So, whats the punchline? You usually need all three. Just not in the same product.
Also Read: How to Choose the Right Healthcare Data Integration Platform
Core capabilities to look for in modern healthcare data integration tools
Most vendor demos look great. Then you hit week 6 of implementation and discover the “connector” is basically a PDF. So here’s what I look for when I’m assessing healthcare data integration platforms with teams.
Connectivity and adapters
Connectivity is where projects live or die. You want proven adapters for the systems you actually run, not the ones on a slide.
- EHRs: Epic, Oracle Health, Meditech, athenahealth, eClinicalWorks. Ask which versions and which integration methods are supported.
- LIS and RIS and PACS: Results, orders, scheduling, DICOM routing, and bidirectional workflows.
- Payers: X12 transactions, payer-specific quirks, and monitoring for failed submissions.
- Devices: RPM platforms, bedside monitors, gateways, and IoT ingestion patterns.
And dont ignore the “boring” stuff: SFTP, VPNs, cert rotation, IP allowlists, and firewall change windows. Those details eat timelines.
Standards support
Standards are the language of healthcare integration. But each shows up in different places, for different reasons.
- HL7 v2: Still the workhorse for ADT, orders, and results. Youll see it everywhere in hospitals.
- FHIR R4: Great for API-based access, apps, patient access, and newer workflows. But its not a magic replacement for HL7 v2 feeds.
- CDA: Think CCD and clinical documents, often used for summaries and transitions of care.
- DICOM: Imaging studies and metadata. Non-negotiable in radiology and cardiology imaging.
- X12: Claims, eligibility, remits, and prior auth plumbing.
Now, here’s the real question: does the tool support the standards and the operational reality? For example, can it handle HL7 v2 custom Z-segments without breaking your mapping UI?
Transformation and mapping
Transformation is where “data exchange” becomes “data you can trust.” You need mapping tools that handle structure, code sets, and business rules.
Look for strong support for terminologies like SNOMED CT, LOINC, ICD-10, and RxNorm. If your platform cant normalize lab codes to LOINC or problems to SNOMED, your downstream analytics and clinical decision support will be noisy at best.
And dont skip validation gates. I like setups where messages are checked for required fields, code validity, and schema compliance before they hit production destinations. Catch bad data early. Always.
Master data and patient matching
This is the section competitors usually gloss over. They shouldn’t.
Patient identity is the backbone of enterprise healthcare data integration. Without a solid MPI strategy, you get duplicate charts, mismatched results, and clinicians losing trust in the data. Thats not theoretical. Ive seen it create real rework in ED and inpatient settings.
So evaluate whether the tool supports:
- MPI integration: Ability to call or sync with your enterprise MPI or identity service.
- Identity resolution: Deterministic and probabilistic matching, configurable thresholds, and survivorship rules.
- Record linkage workflows: Queues for manual review, audit trails, and feedback loops to improve match quality.
If youre a digital health vendor, this matters too. Multi-tenant identity gets complicated fast when patients show up across payers, providers, and device ecosystems.
Orchestration and workflow automation
Integration isnt only moving data. It’s coordinating steps.
Good platforms let you orchestrate workflows like: receive referral, validate coverage, request prior auth, schedule appointment, notify patient, and push status back to the EHR. That means timers, branching logic, human-in-the-loop tasks, and idempotency so you dont create duplicates when something retries.
And yes, you want this without writing 10,000 lines of custom code for every new partner.
Monitoring, alerting, retries, audit trails
This is operational excellence. It’s also where teams earn credibility.
At minimum, your tool should provide:
- Message tracking: End-to-end correlation IDs, searchable payload history, and clear status.
- Retries and backoff: Configurable policies, idempotent delivery patterns, and safe replay.
- Dead-letter handling: Quarantine bad messages, route to triage queues, and support reprocessing after fixes.
- Audit trails: Who accessed what, what changed, and when. This matters for HIPAA and for debugging at 2 a.m.
So ask vendors directly: “Show me how you handle a downstream outage for 3 hours. What breaks? What queues? What alerts fire? What does recovery look like?” If they hand-wave, move on.
Healthcare data integration architecture for enterprises
Architecture is the difference between a system that scales and one that becomes a fragile web of point fixes. If youre serious about healthcare data integration architecture for enterprises, you need patterns that match your org’s complexity and risk tolerance.
Point to point vs hub and spoke vs iPaaS vs event driven
Point-to-point is quick at first. Then it turns into spaghetti. Every new connection increases complexity, testing surface area, and outage blast radius.
Hub-and-spoke is the classic interface engine model: central routing, transformation, and monitoring. It’s proven. It’s common in hospitals. And it still makes sense for a lot of HL7 v2 traffic.
iPaaS brings cloud-native scaling, API management, and reusable connectors. It can be great when you’re integrating SaaS apps, payer services, and multi-cloud workloads. But dont assume it replaces an interface engine automatically.
Event-driven architectures push you toward real-time, decoupled systems. Think Kafka topics for ADT events, or FHIR Subscriptions feeding downstream services. This shines when multiple consumers need the same event stream and you want resilience.
But here’s my opinion: most enterprises end up with a hybrid. And thats fine. The goal is not purity. The goal is reliability and speed of change.
Healthcare data pipeline architecture
A solid healthcare data pipeline architecture usually follows a simple flow: ingest, normalize, store, serve. Simple words. Lots of engineering.
- Ingest: HL7 v2 listeners, FHIR API pulls, X12 gateways, DICOM ingestion, SFTP drops, device streams.
- Normalize: Map to canonical models, terminology normalization, unit conversions, validation gates, and deduping.
- Store: Operational stores for real-time apps, and analytical stores like lakehouse or warehouse for reporting.
- Serve: APIs, FHIR endpoints, downstream feeds, dashboards, and event streams.
Now, if you skip normalization, you pay later. Your analysts will build 14 versions of “encounter,” and none of them will match.
Where APIs, interface engines, and integration platforms fit
Here’s the clean way to think about it:
- Interface engines are great at HL7 v2 routing, transformation, acknowledgments, and operational monitoring.
- API layers are great at controlled access, developer experiences, throttling, and modern app integration.
- Integration platforms sit across both worlds, handling connectors, orchestration, and cross-system workflows.
And your healthcare interoperability architecture should treat these as building blocks. Not as one mega-tool that “does everything.” Those rarely end well.
Tool categories with examples and when to use
Let’s talk categories. Not vendor hype. Categories. Because the right answer depends on your existing stack, standards mix, and operational needs.
Interface engines
Interface engines are the backbone in many hospitals. They excel at HL7 v2, message routing, transformations, and acknowledgments.
Examples: InterSystems HealthShare Health Connect, Rhapsody, Mirth Connect and NextGen Connect, Corepoint, Iguana.
When to use: Heavy HL7 v2 environments, lots of ADT and results traffic, need strong operational tooling, and you want to centralize routing rules.
But watch for this: some interface engines can become “that one box” only two people understand. Document your routes. Version your mappings. Treat it like real software.
iPaaS and integration platforms
iPaaS tools are popular because they connect cloud apps quickly and scale without you managing servers. Theyre often strong at APIs, SaaS connectors, and workflow automation.
Examples: MuleSoft, Boomi, Informatica, Workato, Azure Logic Apps, AWS Step Functions plus integration services.
When to use: Hybrid integration across SaaS, payer services, CRM, scheduling tools, and internal systems. Also great when you need orchestration beyond “transform and forward.”
And yes, you can run healthcare messaging through iPaaS. Just make sure it truly supports HL7 v2 patterns like ACK handling, sequence control, and replay at scale.
Cloud healthcare APIs
Managed healthcare APIs can reduce the pain of standing up FHIR servers, DICOM stores, and HL7 ingestion. You get scalability and managed operations, usually with compliance features baked in.
Examples: Google Cloud Healthcare API, AWS HealthLake, Microsoft Cloud for Healthcare building blocks and Azure Health Data Services.
When to use: You want managed FHIR and DICOM, youre building patient-facing apps, or you need a clean API layer for partners. Also useful for analytics pipelines that start with normalized resources.
But be honest: managed APIs dont automatically solve mapping, identity, or data quality. You still need those layers.
ETL and ELT and analytics integration
Analytics integration is its own beast. You’re optimizing for throughput, history, and governance, not millisecond response times.
Examples: dbt, Fivetran, Matillion, Talend, Informatica, Databricks pipelines, Snowflake-native ingestion patterns.
When to use: Building enterprise reporting, quality measures, cost analytics, risk models, and longitudinal patient records for analysis.
This is where enterprise healthcare data integration often gets real value: reducing manual chart abstraction, improving HEDIS measures, and powering operational dashboards with near-real-time feeds.
HIE and exchange networks and point solutions
Sometimes you need network-level exchange, not just internal plumbing. HIE tools and exchange networks focus on cross-organization data sharing, document exchange, and consent-aware workflows.
Examples: HealthShare, eHealth Exchange connectivity through partners, CommonWell integrations through certified vendors, regional HIE platforms, EMS-to-hospital exchange point solutions.
When to use: External data exchange, transitions of care, community-wide interoperability, and when your org needs to participate in established networks.
Real scenario: an EMS agency sends pre-hospital vitals and narrative to an ED. If that arrives 12 minutes late, it’s basically trivia. The right point solution plus integration into ED tracking can make it actionable.
Also Read: Healthcare ETL Tools: How to Choose the Right Platform for Secure, Compliant Data Pipelines
Security, compliance, and governance
If youre moving PHI, you’re in HIPAA territory. And even if youre not a covered entity, your customers will demand HIPAA-ready controls. No shortcuts.
Encryption, key management, access controls, logging
Baseline expectations:
- Encryption in transit and at rest: TLS 1.2+ for transport, strong encryption for storage.
- Key management: KMS integration, rotation policies, and separation of duties.
- Access controls: Least privilege, role-based access, and ideally SSO with MFA.
- Logging: Immutable logs, searchable audit events, and clear retention policies.
And dont forget environment separation. Ive seen teams accidentally route test messages into production endpoints. Once. They never do it again.
BAAs, data residency, retention, de-identification
Get the paperwork right. If a vendor touches PHI, you’ll need a BAA. Period.
Also ask where data is stored and processed. Data residency can be a deal-breaker for some orgs and some state-level requirements. Retention matters too: do you keep message payloads for 7 days, 30 days, 6 years? Your compliance team will have opinions.
For analytics and ML, de-identification and tokenization are often the practical path. But be careful: “de-identified” in marketing copy can still be re-identifiable in practice if you keep enough quasi-identifiers.
Consent management and minimum necessary
Consent is messy. It’s also unavoidable.
Your integration approach should support consent flags, segmentation where required, and enforcement of the “minimum necessary” principle. Not every downstream system needs full clinical notes when all it needs is an appointment status.
So design your flows to share what’s needed, not everything you can technically send.
How to choose the right healthcare data integration platform
This is the commercial investigation part. And yes, you can do it without a 6-month bake-off if you’re disciplined.
Requirements checklist
Start with reality. Not aspiration.
- Volume: Are you processing 50,000 HL7 messages per day or 5 million? That changes tooling choices fast.
- Latency: Do you need sub-minute delivery for ADT and EMS handoff, or is hourly fine for analytics loads?
- Sources and destinations: EHR, LIS, PACS, payer gateways, RPM devices, CRM, data lake, third-party partners.
- Standards mix: HL7 v2, FHIR R4, CDA, DICOM, X12. Also, how much “non-standard standard” do you expect?
- Data quality needs: Terminology services, validation gates, and exception workflows.
- Identity strategy: MPI integration, match rates, and how you handle merges and unmerges.
- Operations: On-call model, monitoring, replay, and audit requirements.
Write these down as testable statements. “Supports FHIR” is vague. “Can ingest FHIR R4 Patient, Encounter, Observation, and Condition and enforce profile validation” is testable.
Buy vs build and total cost of ownership
Build sounds cheaper until you price the team you actually need: integration engineers, SRE, security, compliance, and 24/7 support coverage. Even a small program can easily be 4 to 8 people when you include on-call rotation and backlog.
Buying isnt cheap either. Licenses, message volume pricing, environment costs, and professional services add up. Ive watched teams underestimate implementation by 30% to 50% because they didnt account for partner testing cycles and firewall work.
So do TCO honestly:
- Licensing and infrastructure
- Implementation services
- Ongoing support and upgrades
- Downtime cost and incident response effort
And ask yourself: do you want to be in the integration tooling business, or in the patient-care and product business?
Vendor evaluation scorecard
I like a simple scorecard with weighted criteria. Not perfect. Just sane.
- Standards depth: Real HL7 v2 and FHIR support, not checkbox support.
- Connector maturity: Proven integrations with your EHR and top partners.
- Mapping and terminology: LOINC and SNOMED mapping support, validation, and testing tools.
- Identity: MPI integration, identity resolution options, and merge handling.
- Reliability: Queues, retries, idempotency, dead-letter handling, and replay workflows.
- Observability: Dashboards, alerting, correlation IDs, and export to your SIEM.
- Security and compliance: BAA readiness, access controls, audit trails.
- Support and SLAs: Response times, escalation paths, and real references.
- Roadmap: Where the product is going in the next 12 to 24 months.
Now, the pro move: ask for two customer references with similar EHRs and similar message volumes. Then ask what broke during go-live. You’ll learn more in 30 minutes than in 3 demos.
Implementation best practices
This is where projects either become a quiet success or a loud mess. Ive been in those war rooms. You dont want that.
Start with a high-value workflow and define data contracts
Pick one workflow that matters. ADT feeds to downstream systems. Lab results to care gaps. Prior auth status back to scheduling. Something that stakeholders will actually notice.
Then define data contracts: required fields, code sets, allowable values, and versioning rules. Treat interfaces like products. Because they are.
And if youre building a broader healthcare data integration architecture for enterprises, use that first workflow to prove your patterns: naming conventions, routing rules, error handling, and monitoring.
Testing, validation, and change management
Testing with real PHI is risky. So use synthetic PHI that still behaves like reality: realistic names, messy addresses, missing phone numbers, duplicate MRNs, and oddball lab panels.
Validate at multiple layers:
- Schema validation: HL7 structure, FHIR profiles, required segments and fields.
- Terminology validation: Are LOINC codes valid? Are units consistent?
- Business rule validation: Does a referral status transition make sense, or did you skip a step?
Now, change management: integrations break when upstream teams change a field “just a little.” Put a process in place. Version your mappings. Require backward compatibility for a window. Youll thank yourself later.
Observability KPIs
If you cant measure it, you cant run it. Observability is not optional for healthcare integrations, especially when you’re supporting ED and inpatient workflows.
KPIs I recommend:
- Message success rate: Percent delivered successfully end-to-end. Track by interface and destination.
- Time-to-deliver: P50, P95, P99 latency. Yes, all three. Averages lie.
- Error budget: Define an SLO like 99.9% delivery within 2 minutes for ADT to downstream consumers.
- Replay volume: How often are you reprocessing messages? It’s a leading indicator of upstream instability.
- On-call load: Pages per week by integration. If one interface causes 60% of pages, fix that first.
And build an incident playbook. Who gets paged? How do you pause a route? How do you reprocess safely? When do you notify clinical ops? This is where trust is won.
FAQs
What’s the difference between HL7 v2 and FHIR?
HL7 v2 is message-based and has been the default for decades in hospitals. It’s great for event notifications like ADT, orders, and results, but it’s also famously flexible, which means lots of site-specific variation.
FHIR is resource-based and API-friendly. It’s better suited to modern apps, patient access, and standardized data access patterns. But many real-time hospital workflows still run on HL7 v2 today, and theyre not disappearing overnight.
Do I need an interface engine if I have an iPaaS?
Maybe. If your environment is heavy HL7 v2 with complex ACK patterns, lots of custom segments, and 24/7 operational monitoring needs, an interface engine can still be the cleanest tool for the job.
That said, some iPaaS products can handle healthcare messaging well, especially when paired with strong observability and a clear reliability design. Many orgs run both: interface engine for hospital messaging, iPaaS for SaaS and workflow orchestration.
How do I integrate unstructured notes and imaging metadata?
For unstructured notes, you typically ingest documents via CDA, HL7 v2 MDM, or FHIR DocumentReference, then store them in a document repository or content service. If you need to extract meaning, you’ll likely add NLP tooling, but keep the original text as the source of truth.
For imaging metadata, DICOM is the starting point. You can ingest DICOM headers, map key fields into a searchable index, and expose them through APIs for downstream workflows. Many teams keep pixel data in a DICOM store and push only metadata into analytics systems to control cost and access.
Choosing healthcare data integration tools isnt about picking the most popular logo. It’s about matching capabilities to your standards mix, your operational reality, and your long-term architecture.
Focus on the fundamentals: connectivity that works with your real systems, deep support for HL7 v2 and FHIR and DICOM and X12, strong mapping with terminology normalization, and a serious approach to patient identity resolution. Then demand reliability: queues, retries, replay, audit trails, and measurable SLOs.
And if you take one thing from this: design integrations like products. Define data contracts, test with realistic synthetic data, instrument everything, and make observability part of day one. Your clinicians wont see the integration layer. But they’ll feel it every time it fails.