Hospitals rely on systems that keep care, revenue, and reporting in motion. Many of those systems run on aging stacks. You feel the drag in slow change cycles, downtime, and staffing gaps. You also face rising security risk and new compliance rules. Legacy healthcare system modernization gives you a way forward without ripping out everything at once. This guide shows you how to set the strategy, choose patterns, quantify risk, and move in controlled sprints.
According to the American Hospital Association, the nation includes over 6,100 hospitals, which makes modernization a scale problem and an operations problem, not only a technology project. Security pressures rise as well. IBM reports healthcare breach costs at multi-million USD levels per incident, which links technical debt to real financial exposure. You need a plan that lowers risk while preserving core workflows and data.
Why You Need Legacy Healthcare System Modernization Now
Modernization work stalls when leaders fear downtime, budget spikes, and clinical disruption. You break through by reframing the goal. The goal is not a shiny new platform. The goal is stable delivery, faster change, stronger security, and measurable outcomes. The modernization of the legacy healthcare system aligns those goals with a roadmap that respects production realities.
A second push comes from policy. As per ONC’s HTI-1 program, certified modules move to USCDI v3 by January 1, 2026, which means your data contracts, mappings, and validation rules must keep pace. A third push comes from operations. Censinet summarizes a study placing downtime at 7,500 USD per minute on average for hospitals, which turns reliability into an executive priority. And research from Pegasystems highlights enterprise losses near 370 million USD per year tied to outdated systems and failed transformations, which underlines the need for a disciplined approach.
What “Good” Looks Like: Outcomes That Guide Every Decision
Legacy healthcare system modernization succeeds when it delivers outcomes leaders track every month. Set clear targets and keep them visible.
- Time To First Value decreases from quarters to weeks.
- p95 integration latency falls and stays under defined SLAs.
- First-pass data quality rises for target flows.
- Unplanned downtime drops, along with mean time to resolve.
- Security posture improves with short-lived tokens, mTLS, and immutable audit.
- Cost to serve declines for integrations, tickets, and after-hours support.
Each metric becomes a gate for release promotion. You move forward when outcomes hold or improve.
A Strategy That Extends Life Without Freezing Innovation
You extend the life of core systems and still deliver digital programs. Legacy healthcare system modernization aligns old and new with a common integration backbone, a controlled migration plan, and a standard way to measure risk.
Principles You Stick To
- Production First: protect clinical and revenue operations during change.
- Interface-Led: lift and shift interfaces early to improve reliability fast.
- Data Contracts: lock FHIR as the canonical model where practical, with HL7 v2 and X12 at the edges.
- Security by Default: OAuth, mTLS, least privilege, and immutable logs for every hop.
- Quality in Flight: validation and enrichment live inside pipelines, not after loads.
- Incremental Delivery: small, reversible changes with rollback and feature flags.
These principles turn legacy healthcare system modernization into an operating model instead of a risky one-time project.
Architecture Patterns That Lower Risk and Raise Speed
Choose patterns that respect vendor realities and let teams ship value early. Each pattern supports the modernization of the legacy healthcare system without large outages.
1. API Façade in Front of Legacy
Wrap legacy apps with a stable API layer. Publish FHIR resources where possible. Keep legacy protocols behind the façade. Map, validate, and enrich at the edge, then expose clean contracts to your product and analytics teams. This pattern reduces change inside the core while unlocking new use cases outside.
2. Event-Driven Backbone For Shared Truth
Adopt an event backbone for Patient, Encounter, Appointment, Order, Result, and Claim. Publish events after acceptance in legacy or modern systems. Consumers subscribe to the truth instead of polling many endpoints. Use idempotency keys and payload fingerprints to avoid duplicates. This pattern supports gradual moves without breaking downstream workflows.
3. Strangler Pattern for Workflows
Migrate one workflow slice at a time. Route traffic for a narrow path to a new service while the rest stays in legacy. Grow new slices until legacy hosts fewer critical paths. This pattern fits scheduling, orders, and prior authorization especially well.
4. Data Lakehouse With Strong Lineage
Mirror production data to a governed lakehouse for analytics and AI. Preserve provenance, rule versions, and consent for each record. Feed models with trusted inputs while you modernize sources. This protects analytics teams from schema drift inside legacy systems.
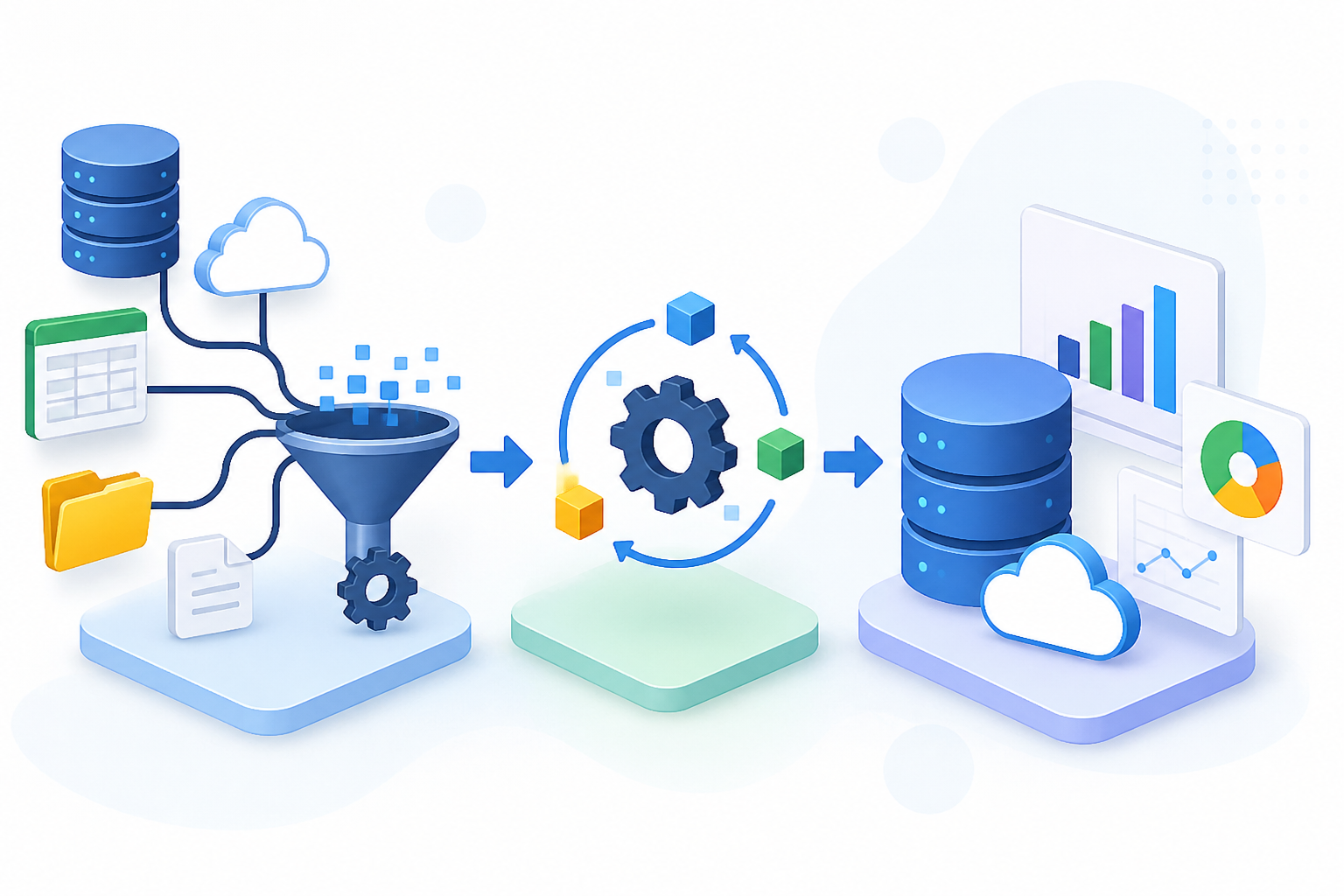
The Five-Layer Reference Stack for Legacy Healthcare System Modernization
Use a clear stack so teams move faster and avoid repeated debate.
- Connectivity: REST, FHIR, HL7 v2 over MLLP, X12, SFTP, and webhooks.
- Contracts: FHIR R4 profiles for core domains, JSON Schema for partner APIs, HL7 v2 profiles, and C-CDA guides for legacy.
- Mapping and Terminology: visual, versioned transforms with unit tests per field. Terminology services for LOINC, SNOMED CT, RxNorm, ICD-10-CM, and NDC.
- Quality and Rules: schema validation, code normalization, cross-resource checks, and workflow gates.
- Observability and Security: correlation IDs, structured logs, traces across hops, OAuth, mTLS, least privilege, immutable audit, and short token lifetimes.
This stack becomes the foundation for every clinical, RCM, and analytics flow. It also anchors your USCDI v3 move.
Risk Model: Quantify Before You Move
Leaders approve plans that link risk to numbers. Before each migration step, score risk across five lenses. Then pick the next slice based on total impact and ease.
- Operational Exposure: downtime impact, reroute options, and on-call coverage.
- Data Criticality: chart impact, coding impact, and claim dependencies.
- Security Posture: current auth model, key age, and audit gaps.
- Vendor Constraints: contract limits, change windows, supported versions.
- Team Readiness: owner depth, test coverage, and runbook quality.
Refer back to the AHA hospital count and IBM breach costs to ground your scoring in real system scale and dollar exposure.
Data Quality Rules That Stop the Spread Of Bad Inputs
Technical debt shows up as messy data. Fix it where data moves. Legacy healthcare system modernization succeeds when rules fire early and consistently.
- Identity: require two strong identifiers to create a record, with tunable match thresholds and a stewardship queue for low confidence cases.
- Orders: enforce encounter links, ordering provider, and coded reason.
- Results: require LOINC codes, units, reference ranges, and method when present.
- Medications: use RxNorm ingredients and strengths for reconciliation and exchange.
- Claims: validate CPT, ICD-10-CM, pointers, NPI, payer edits, and attachments.
Track first-pass success, auto-heal share, and dead-letter queue time to clear. Publish trends so teams see progress.
Security and Compliance Built Into Every Hop
Modernization raises risk unless you build a stronger security baseline as you go.
- Short-lived tokens and least privilege for all services.
- Mutual TLS between trusted systems, including partner endpoints.
- Immutable audit on each read and write with redaction where required.
- Key rotation as code, with alarms for stale secrets.
- Consent and purpose-of-use tags linked to each message.
Security work supports reliability. Downtime and breach costs remain high across healthcare, and downtime minutes stack up fast. Anchor decisions to the 7,500 USD per minute reference and the IBM breach cost analysis to secure support for guardrails.
Choosing the Right Migration Slices
Legacy healthcare system modernization moves faster when you select slices that create visible value with limited blast radius.
- Eligibility and Coverage: move to stable APIs with caching and backoff.
- Scheduling: publish FHIR Appointment and related resources with adapters for legacy SIU.
- Orders and Results: standardize to FHIR ServiceRequest and DiagnosticReport with Observation linking.
- Prior Authorization: route through a rules engine that supports FHIR APIs and X12 278 as needed.
- Documents: shift to DocumentReference with hashes and MIME checks.
- Claims: pre-validate with payer edits before 837 export, link authorization IDs, and capture denial reasons as structured codes.
Each slice includes tests, runbooks, and dashboards before go live.
KPI Library: Metrics That Keep Everyone Honest
Define a stable set so leaders track the same truth each month. Legacy healthcare system modernization thrives when KPIs align to operations and outcomes.
Reliability
- p95 end-to-end latency by flow and partner.
- Delivery success and retry rates.
- Dead-letter queue depth and time to clear.
- Time to ACK by EHR, payer, and HIE endpoints.
Quality
- First-pass validation success rate.
- Completeness gate violations by type.
- Terminology lookup miss rate.
- Duplicate rejection rate and steward turnaround.
Security
- Failed auth attempts by endpoint.
- Token age distribution and expired scope count.
- Audit event completeness rate.
- Key rotation on-time percentage.
Operations
- Tickets per 10,000 messages.
- Mean time to detect and resolve.
- On-call pages per shift.
- Cost to serve for target flows.
Business Impact
- Clean-claim rate and days in A/R for targeted services.
- Prior authorization cycle time and approval rate for targeted services.
- Readmission rate and ED revisits for targeted cohorts when linked programs go live.
The Six-Stage Roadmap for Legacy Healthcare System Modernization
Use this roadmap to guide planning and execution. Each stage produces value and reduces risk.
Stage 1: Baseline and Business Case
- Inventory systems, interfaces, and message classes.
- Map vendor versions, contract limits, and change windows.
- Measure current reliability, quality, and security metrics.
- Identify top five risks and top five fast-win slices.
- Build a scorecard for executives with targets and owners.
Anchor the case with external references. As per ONC, USCDI v3 compliance arrives on January 1, 2026, and downtime averages 7,500 USD per minute, which supports investment in stability and data upgrades.
Stage 2: Establish the Integration Backbone
- Stand up secured connectivity for REST, FHIR, HL7 v2, X12, and SFTP.
- Enforce OAuth and mTLS for all partners, even legacy.
- Assign correlation IDs and tracing across hops.
- Configure dashboards with p50 and p95 latency and delivery success.
- Create a dead-letter path with privacy controls and replay tools.
This foundation lifts reliability before any major migration.
Stage 3: Quality Gates and Terminology
- Enable schema checks for HL7 v2 profiles and FHIR resources.
- Turn on code normalization for LOINC, SNOMED CT, RxNorm, and ICD-10-CM.
- Define completeness gates for each target slice.
- Route failures with sample payloads and runbook links.
- Publish first-pass rates and auto-heal share each week.
Quality gates reduce rework and slow leak costs while legacy remains in play.
Stage 4: Migrate Priority Slices
- Move target slices behind an API façade and event backbone.
- Run canary traffic on a small cohort before full shift.
- Lock rollback steps and feature flags for safe exits.
- Update runbooks and train owners for new alerts and dashboards.
- Measure outcome deltas against baselines and publish results.
This stage turns the roadmap into visible wins: fewer duplicates, faster approvals, cleaner claims.
Stage 5: Harden Security and Audit
- Shorten token lifetimes and tighten scopes.
- Automate key rotation and certificate renewals with alarms.
- Expand audit with before-after values and actor for sensitive fields.
- Run breach tabletop drills with payload samples and timelines.
- Share audit views with compliance and internal audit.
Security improvements often unlock stalled vendor approvals and reduce insurance exposure.
Stage 6: Expand and Retire
- Extend the same patterns to more services and regions.
- Retire non-critical legacy interfaces once traffic falls below thresholds.
- Archive with retention policies, lineage, and retrieval plans.
- Refresh the business case with measured savings and risk reduction.
- Plan the next cycle with USCDI, payer policy, and vendor upgrades in view.
By this point, legacy healthcare system modernization has lowered outages and support load while enabling new features without large rewrites.
Runbooks That Keep Teams Calm During Change
Every frequent failure deserves a short runbook. Keep steps simple and test them during on-call drills.
- Expired Certificates: symptoms, last rotated date, renewal steps, verification command, and partner contact.
- Schema Drift: how to diff payloads, patch maps, re-validate, and replay.
- Partner Timeouts: backoff settings, temporary queue caps, and escalation steps.
- Terminology Gaps: how to add codes, warm caches, and recheck failures.
- Auth Scope Errors: rotate keys, update scopes, and run a smoke test.
Link each runbook inside alerts so responders move fast.
Data Retention, Archiving, and E-Discovery
Modernization often exposes weak retention logic. Fix it as part of the roadmap.
- Store audit and lineage with retention rules by domain.
- Keep de-identification filters for analytics exports.
- Maintain legal hold processes for investigations.
- Document retrieval and export steps for regulators and payers.
Good record hygiene reduces risk during audits and security events. It also accelerates analytics and AI work by providing trusted sources.
Budget and Staffing: Models That Work in Health Systems
Legacy healthcare system modernization needs a realistic plan for people and dollars.
- Fund the backbone and quality gates before feature work.
- Reserve budget for vendor certifications, test environments, and partner fees.
- Assign a lead engineer, a data quality owner, and a security owner for each slice.
- Cross-train analysts and SREs on FHIR contracts, HL7 profiles, and trace tools.
- Track run-rate savings from auto-healing, fewer incidents, and faster releases.
Share monthly scorecards so finance sees fewer tickets, fewer on-call pages, and lower rework hours.
Avoid These Pitfalls During Legacy Healthcare System Modernization
- All-At-Once Rewrites: replace slices, not entire domains, to lower blast radius.
- Late Quality Checks: validate at ingress, not in a nightly job.
- Portal Sprawl: surface functions inside current workflows where possible.
- Weak Identity Matching: tune thresholds and work the suspect queue daily.
- No Attribution: tie outcome improvements to specific exchanges and rules.
- Silent Drift: watch for schema or code changes and alert on diffs.
Consistent habits and narrow scopes build trust with clinical and revenue leaders.
How Vorro Helps You Deliver Modernization With Less Risk
Vorro’s VIIA platform supports the modernization of the legacy healthcare systems with a managed, no-code approach that replaces custom scripts with governed pipelines.
- No-Code Mapping: visual, versioned transforms for FHIR, HL7, C-CDA, and X12 with per-field tests.
- Quality in Flight: schema checks, code normalization, and workflow gates to stop bad data early.
- Observability: correlation IDs, traces across hops, p95 latency metrics, and run-time dashboards.
- Auto-Healing: targeted retries, schema drift fixes, and suppression for flapping endpoints.
- Security and Audit: OAuth, mTLS, least privilege, immutable logs, and exportable lineage.
- USCDI v3 Readiness: profiles and rules aligned to the 2026 baseline so teams avoid a last-minute scramble.
With VIIA, legacy healthcare system modernization progresses in weeks for the first slices, then scales across service lines with repeatable patterns.
The 90-Day Action Plan for Legacy Healthcare System Modernization
Use this plan to prove value, reduce risk, and build executive confidence.
Day 1–30: Foundation and Fast Wins
- Stand up the backbone for REST, FHIR, HL7 v2, and X12 with OAuth and mTLS.
- Instrument correlation IDs and p95 latency across top five flows.
- Launch dashboards and set alert ownership.
- Turn on schema validation for two flows with a dead-letter path and replay tools.
- Publish a one-page scorecard with baseline metrics.
Days 31–60: Quality and First Slices
- Enable code normalization for LOINC, SNOMED CT, RxNorm, and ICD-10-CM.
- Set completeness gates for eligibility and scheduling.
- Migrate eligibility behind the API façade with caching and backoff.
- Run canary traffic for scheduling with FHIR Appointment and legacy SIU adapters.
- Report improvements in error rate, latency, and ticket volume.
Days 61–90: Expand and Harden
- Move orders and results with FHIR ServiceRequest and DiagnosticReport.
- Add denial pre-edits for a pilot claim set and link authorization IDs.
- Shorten token lifetimes and automate key rotation with alarms.
- Drill incident response for schema drift and certificate expiry.
- Publish outcome deltas and next quarter’s slices, retire one legacy interface with a rollback option.
This plan gives leaders early proof and a path to sustained outcomes. It also aligns the team to the 2026 USCDI v3 shift while lowering downtime risk, which runs 7,500 USD per minute.
Your Playbook for Legacy Healthcare System Modernization
Legacy healthcare system modernization extends the life of core platforms while you deliver new services with lower risk. You make progress by standardizing contracts, enforcing quality in flight, instrumenting performance, and moving small slices with clear rollbacks. You also protect the business with strong security and audit as the default behavior.
Get a tailored roadmap for two high-impact slices, with contracts, rules, and dashboards mapped to your environment. See how legacy healthcare system modernization with VIIA reduces incidents, accelerates delivery, and prepares you for USCDI v3.
Anubhav is a content marketer who helps brands grow without sounding like their content was written by a committee. He is drawn to layered storytelling and long narrative arcs, and brings that same depth to complex, industry-specific content. He enjoys turning technical material into stories people can actually follow. When he is not doing that, he builds AI agents to handle the parts of content creation that everyone pretends to enjoy.