By Akshita Kohli · November 7, 2025
More Than Just Servers: Why Integration is Your New Compliance Frontier
As a Chief Technology Officer in healthcare, your role extends far beyond managing servers. You are the ultimate custodian of patient trust and the final firewall against regulatory risk. You know that compliance isn’t just a box to check; it’s the fundamental, non-negotiable layer protecting every single patient interaction.
In today’s complex digital world, patient data is fragmented. It resides across cloud applications, legacy systems, and dozens of vendor portals. If you can’t see and manage all of that data flow, you can’t secure it. This reliance on manual tracking and spreadsheet audits for data governance is not just inefficient; it’s an existential threat.
Let’s face a tough truth: the average cost of a healthcare data breach now exceeds $10 million per incident. This massive figure covers fines, legal fees, the crushing impact on your organization’s reputation, and lost business. All these risks land squarely on the disconnected technology infrastructure you oversee. That’s why a robust Data Integration Platform is no longer a “nice-to-have”—it’s a survival mechanism for compliance.
The market is full of tools. Your real challenge is finding the right platform. You need one that will:
- Connect with your messy, often legacy, IT ecosystem.
- Scale as you grow.
- Provide a single, verifiable source of truth about data access and movement.
This checklist is built specifically for you, the technical leader. We’re cutting through the marketing hype to evaluate these solutions based on the technical merits that genuinely enable and streamline healthcare data security and compliance.
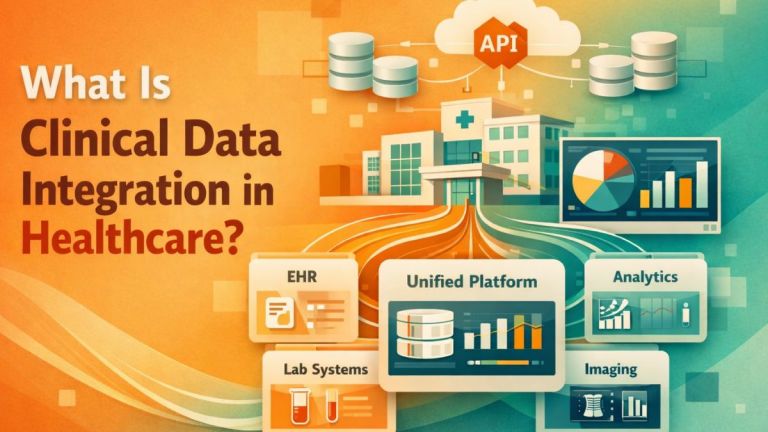
What is a “Compliance-Enabling” Data Integration Platform?
At its core, a modern healthcare Data Integration Platform (often called an iPaaS) is smart software. It uses sophisticated logic to connect disparate systems and centralize control over all data flowing through your organization.
Think of it as your single gateway for PHI management. This includes ensuring data is encrypted, logged, and governed according to the latest standards (HIPAA, GDPR, HITRUST).
The stakes couldn’t be higher. Data volume is exploding, new regulations are always emerging, and the threat landscape changes daily. Disconnected systems guarantee human error and create unacceptable delays between a policy change and its enforcement. Integration is the only way to achieve the continuous visibility needed to be audit-ready.
The CTO’s Technical Vetting Checklist
1. Data Integration and Interoperability
Core Question: Can the platform genuinely connect with our messy, complex, and often legacy environment?
In healthcare, data is always fragmented. It lives across multiple Electronic Health Records (EHRs like Epic and Cerner), financial systems, imaging archives (PACS), and countless vendor applications. An integration tool is useless if it can only see a fraction of your data. As the CTO, you need to demand absolute technical clarity on connection methods.
Key Technical Requirements:
- Protocol Agnosticism: The solution cannot rely only on modern APIs (like FHIR). It must handle the plumbing of older protocols (HL7, EDI), flat files, and direct database connectors. This is how you bridge the gap between your old and new systems.
- Bi-Directional Flow: Integration shouldn’t be read-only. The tool must be able to receive data (like access logs) and also enforce policies (like automatically halting data flow based on a compliance flag).
- Data Normalization Engine: This is essential. The platform needs to ingest data from different sources and standardize it into a single, usable data model. If it fails here, your compliance dashboards will be comparing apples and oranges, making risk assessment impossible.
- Non-Invasive Architecture: The best solution acts as a secure, transparent layer over your existing systems, not inside them. This minimizes risk and avoids disruptive, costly changes to your core clinical applications.
2. Real-Time Data Monitoring and Compliance Visibility
Core Question: Does the solution provide genuine, continuous oversight, or just outdated, periodic snapshots?
A compliance report generated yesterday is already too late. Regulators and your risk profile require constant monitoring of data access and movement. You need a system that operates in the moment, not in the past.
Key Technical Requirements:
- Immutable Audit Trail: The platform must automatically and indelibly log every critical data event: every access, every PHI transfer, and every policy enforcement action. This creates a verifiable, cryptographic audit trail that is always ready for a regulatory inquiry.
- Anomalous Behavior Detection: This capability goes beyond simple rule-setting. The solution should use advanced pattern recognition to flag actions that simply don’t look right (e.g., a finance user suddenly trying to access a massive volume of patient clinical notes). This is how the machine helps you catch risks before your team even notices.
- Automated Response Workflows: A sophisticated platform doesn’t just alert you; it initiates pre-defined action. If the system detects a suspicious, mass download of PHI being pulled for transfer, the platform should automatically lock the associated integration or halt the data flow, then alert the security team.
- Low Latency Processing: The platform has to be fast. “Real-time” data governance means processing latency must be measured in seconds, not hours, to ensure immediate risk mitigation when data moves.
3. Scalability, Security, and Governance
Core Question: Is the architecture robust enough to handle petabytes of sensitive data while maintaining airtight security?
As a CTO, your concern isn’t today’s data volume, but it’s next year’s. Your integration platform must scale horizontally without causing performance problems or, worse, introducing new security vulnerabilities.
Key Technical Requirements:
- Cloud-Native Architecture: Look for solutions built on modern, secure cloud infrastructure (AWS, Azure, GCP) with demonstrable high availability and fault tolerance. You must be able to scale computing and storage on demand.
- Zero-Trust Security Model: The platform itself must adhere to the highest security standards. Data must be encrypted at rest and in transit. Internal access should follow a strict least-privilege principle, even for internal administrators.
- Data Residency and Sovereignty: You must confirm that the solution meets all specific requirements for where patient data has to reside. This is a critical concern for compliance with international (GDPR) and various state-level regulations.
How to Conduct a Deep Technical Vetting
You cannot take a vendor’s glossy slide deck at face value. A rigorous technical vetting process is essential. You need to lead this alongside your VPs of Engineering and Security.
- Demand a Detailed Data Flow Diagram: Get them to show you exactly how data moves from your source systems, through their platform’s data processing, into their data model, and out to the final systems. The architecture must be transparent and logical.
- Run a Controlled Proof of Concept (PoC): Never commit to a full deployment without a targeted PoC. Select a single, high-risk workflow (like tracking user access across your most sensitive systems). Then, measure the solution’s performance, accuracy, and latency against your current manual process.
- Review Their SOC 2 Type 2 Report and BAA: Treat the vendor as an extension of your security team. A robust SOC 2 Type 2 report is non-negotiable. Their Business Associate Agreement (BAA) must clearly define their responsibilities regarding PHI security. This is a contract of trust.
- Evaluate Customization and Adaptability: While integration should be automated, healthcare is rarely one-size-fits-all. The platform should offer flexible, low-code/no-code tools to quickly customize data models and build new governance rules without needing months of expensive professional services.
A Quick Example: The Power of Proactive Integration
One regional hospital system was drowning in compliance overhead related to physician credentialing. The manual checking process was error-prone and only happened monthly, creating a huge liability gap. They implemented a modern integration platform.
They leveraged its advanced connectivity to link their HR system, credentialing software, and state/federal exclusion databases in real time. The system automatically checked provider data daily and immediately flagged any provider whose status had changed.
The result? They cut administrative time by 90% and, more importantly, reduced the high-risk compliance window from 30 days to less than 24 hours. The CTO successfully demonstrated that the cost of the system was vastly outweighed by the risk mitigation of avoiding just a single violation.
Conclusion: This Is a Strategic Imperative
The decision to adopt a healthcare data integration platform is one of the most consequential technology choices you will make. It’s an investment in risk mitigation, operational efficiency, and, most crucially, the trust that defines your entire relationship with patients.
The right platform doesn’t just manage risk; it enables innovation by giving you the confidence that your technology foundation is secure and rock-solid.
Your Final Takeaways:
- Integration is King: Prioritize solutions that can flexibly and non-invasively integrate with your entire, complex data ecosystem, from legacy EHRs to modern cloud applications.
- Demand Continuous Visibility: Always choose real-time, automated oversight of data movement over periodic reporting to ensure you are always audit-ready.
- Verify Scalable Security: Ensure the platform is built on a zero-trust, cloud-native model that can demonstrably scale to handle your organization’s future data growth securely.
- The BAA is a Contract of Trust: Scrutinize their security certifications and Business Associate Agreement. They are your partners in protecting PHI, and that partnership must be legally ironclad.